Table of Contents
Shared Hosting: A Guided Explanation
Ever wondered what shared hosting really means? Or maybe you already have a pretty good idea, but don’t really understand the specifics.
In this article we are going to help clear up this topic, starting with the following:
What is Shared Hosting?
Shared Hosting: A Guided Explanation:. This may sound strange at first – but stick with me… Imagine a building. Specifically, an apartment building. We’ll call this building “Webhosting Server.” You don’t own the building. However, you might rent an apartment from the person who does own the building.
After you’ve met the requirements, signed the forms, paid the fees, and receive your key: you are permitted to move into your new apartment.
There are some rules, though. You’ve got neighbors. You probably don’t want to practice your drum solos in the middle of the night. You also can’t take a sledgehammer to your walls and start ripping out the cabling. These things will affect the people you live next to. But, you’ve still got the key. You get to decide who comes in and who stays out. You can shut all the windows, lock all the doors, or leave it wide open and welcome all visitors if you feel like that’s a good thing for you to do. But you can only do it in YOUR apartment.our landlord may get a little upset if you end up welcoming in the wrong people and disturbing the neighbors, though.
However, within the confines of your apartment, you’re mostly free to do whatever you want on the inside. You can decorate, redecorate, furnish, unfurnish, paint, cook, exercise, sleep.. you still get to make it yours. Read more about Shared Hosting: A Guided Explanation
Certain things need for shared hosting
That said… you have to rely on your landlord to get certain things done.
Need your air conditioning unit repaired?
Change the locks on your door?
Fix the plumbing?
Leaky roofs?
Tap water coming out pink and gooey?
These things usually mean that it’s time call the landlord.
Now that you’ve got your apartment all arranged, you want a website.
Shared Hosting: A Guided Explanation:. Mostly, you just want to make a website where you can post clips of your drum solos for your friends to listen to. It’s not a big deal or anything.
You’re not sure how that all works, but you know that if you google “host a website,” you get a lot of results. Read more about Shared Hosting: A Guided Explanation
Every hosting site you come across is going to have a different name for it, but ultimately you have two options:
A dedicated option
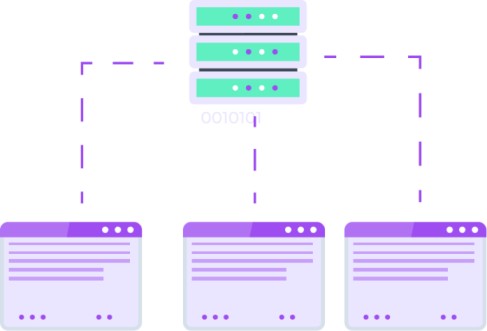
- Having a dedicated service means that you get the apartment building all to yourself.
- A dedicated server is usually a powerful (and expensive) computer, built for the purpose of hosting a lot of websites, or maybe one particularly heavy-duty website.
A shared option
- Having a shared service means that you’re just renting space from it.
Obviously, shared services are going to be a lot cheaper than
buying the whole building.
You could technically run your own website hosting business with a single dedicated server.
In other words, it’s what you might call overkill.
Particularly when it comes to hosting a simple, static website whose primary purpose is to share your drum solos.
This is where shared hosting can help. Read more about Shared Hosting: A Guided Explanation
Shared hosting saves you from having to manage, configure, administer, and pay for a full-fledged, datacenter-hosted, dedicated web hosting server.
Hey, maybe you have great ambitions for your site, and you’ve even got the funds to back it up. If that’s the case, maybe you do want to look into dedicated hosting. Who am I to make assumptions?
However, there are many, many scenarios in which shared hosting is a much more viable and cost-effective option. By purchasing a shared hosting plan, you’re renting space from that server, so that you can host your website inside it, just like that apartment you moved into earlier.
The administrator sets your limitations, policies, and the kind of environment you have access to. You might have a specific amount of space to put your files in, or a limit on how much stuff you can send back and forth over the internet per month, or restrictions on how much of the server’s supplies you get to use.
This is all part of the hosting service selection process.
Who you choose to purchase shared hosting from, what they’re offering, and how much they’re charging for it are all going to be important factors for you to consider.
After all, they’re going to be your website’s landlord for as long you stick with them.
Read more about Shared Hosting: A Guided Explanation
So, you've got neighbors?

It is a shared hosting service, after all. You’re hosting your website on a server that’s also hosting other people’s websites.
This usually doesn’t affect you. If you chose wisely, and you’ve got a knowledgeable, reliable server administrator, then your environment should be secured and isolated in such a way that you never really have to deal with the other patrons occupying the server.
However, if somehow your chosen hosting provider finds out that you’re somehow abusing your resources, then that does affect your web host neighbors.
The provider and the administrator have provided you with this personal space, and as we mentioned earlier, there’s a lot you can do with that.
If you’ve set up an insecure environment (remember the analogy about leaving the doors and windows in your apartment wide open all day and night?), you might find that you quickly become targeted by malicious users.
Even with all the security measures set in place by the administrator, the online security world is a constantly evolving animal.
So, unbeknownst to you, you may have had your email information compromised, or your database compromised, as a result of a security flaw in your website.
Now, you’ve got spam coming from your email accounts, and your database is being used for illicit purposes without your participation.
Despite the fact that you’re not intentionally performing these heinous acts, you’ll still need to address the problem.
By abusing your account, voluntarily or involuntarily, you are potentially impacting your fellow shared hosting server-neighbors’ experience as well.
For that reason, an administrator may be forced to take measures to lock down your account until you’re able to resolve the issue.
The moral of the story is that, even though you have a system administrator that is hopefully doing what they can to secure the host environment, you’ll also need to do your part to be a responsible and proactive shared hosting customer. Read more about Shared Hosting: A Guided Explanation
Being Proactive
So, what can I do to be a proactive shared hosting customer?
Luckily, you won’t need a battalion of tanks (hopefully?)… or any military involvement at all, really.
You will, however, need to understand your website.
You can start by asking yourself these basic questions:
• Am I use a Content Management System. (CMS)?
• Are you using an SSL certificate.?
• Am I using solid passwords.?
• Is there any way for users to input information into my website? (contact forms, search bars..).
• What are my website’s file permissions?
• Do I know who my hosting provider is, and how to contact them?
Are you using a Content Management System (CMS)?

Common CMS platforms include WordPress, Joomla, Drupal, Magento, Prestashop, Typo3… there’s a lot of them out there. WordPress is by far the most popular of these.
These CMS’ exist to make the creation and maintenance of a website easy, even if you don’t know how to write code.
This is a very important question because it drastically affects how you should be approaching your security.
The most important part of maintaining a secure CMS installation involves keeping your software and your plugins up to date.
It is of vital importance to keep WordPress core, plugins and themes updated. Once an update is released, it needs to be applied as soon as possible to close any security holes.
Functional problems with updates must be considered. It is possible that an update will break some of the functionality so a backup is recommended before updating the core.
Need some help locking down your CMS? There’s probably a guide for that.
Here's a handful of handy resources you can take advantage of:
WordPress
OWASP WordPress Security Implementation Guide [OWASP]
WordPress
Hardening WordPress [Official WordPress Codex]
General
How to Secure your CMS [MalwareBytes]
General
A Security Overview of Content Management Systems [Detectify]
Joomla
Security Checklist [Official Joomla! Documentation]
Drupal
Securing Drupal 8 [Official Drupal Documentation]
Am I using an SSL Certificate?

An SSL certificate is a big deal. It secures the transfer of data – like payment information, account details, passwords, or anything else someone might submit on a form – when passing it between the user and your website.
In the old days, this was usually something you’d just see on bank websites, e-commerce sites, or other similarly sensitive environments.
Now, everyone is encouraged to secure their sites with SSL. Not only is it a smart decision, but you might also be able to do it for free.
So, when we say SSL, we’re really referring to SSL/TLS (Secure Sockets Layer/Transport Layer Security). This is what’s actually encrypting information between a visitor’s browser and the server that hosts your website.
If we wanted to really get right down to the scary words, we might say that this protects you against electronic eavesdroppers.
Well.. it does. Electronic eavesdroppers exist, and they are pretty scary, at least in principle. They might also be physically scary, in the way that zombies and ghosts are scary. I have no way of knowing for sure.
I do know that the impact of their actions is scary, though. Identity theft, password leaks, data compromises, bank account access, and any other number of awful deeds can be committed through simple interception of unsecured internet traffic.
In summary, securing your website with an SSL certificate is a good thing. Consider it.
Am I using solid passwords?

Create tough passwords. Use password generators and password management applications (trusted ones, of course).
Abandon that lofty goal of being able to remember all of your passwords. Don’t use the same password for everything.
I’m sorry, but the time when that was realistic has long since passed us by.
Now, we live in a time where brute forcing and dictionary attacks are a threat. A time where compromised passwords will immediately be tested on a thousand other popular web services to check if you used it anywhere else.
You don’t need to establish 8-factor authentication using 8 different, 128,000-character passwords that are generated on 8 separate devices and updated every 8 seconds to create a secure environment.
…however, extra factors are an excellent idea.
This is particularly useful if you frequently use a single account to log into multiple services (such as logging in with Facebook or Google), making the potential impact of a compromise even bigger.
In this situation, you want to do everything you can to make sure that the parent account remains as secure as possible. One way to help with this is to utilize 2-factor authentication.
So, where possible, do use 2-factor authentication.
factor authentication brings security into a physical medium that prevents you from being subjected to a compromise solely based on values stored digitally.
Is there any way for users to input information into my website?

Most modern websites handle user input of some kind. These websites are inherently susceptible.
Susceptible to what?
Allowing users to submit information from your site is providing them with a kind of direct path to performing actions behind the scenes. Usually, you control this. You make a contact form so people can.. contact you.
You don’t make a contact form for people to change user passwords in your otherwise inaccessible MySQL database, yet that’s exactly what can happen. This particular method of compromising a site or a server is called SQL injection.
A query (instructions) might have parameters (data) inserted into it that end up being treated like instructions, usually for malicious purposes.
A malicious user might exploit this by telling an otherwise innocuous form, like a data entry form, to instruct the database to return every user’s details.
Definitely not the intended purpose.
What are my website's file permissions?

Your server has users and groups.
Files on your website are owned by a user and associated with a group. Users are members of groups.
Access is given to files based on its owner, its group, and by one other value: Everyone.
You can change what the file’s owner, group, and… everyone else can do to each file and each folder. That might just involve letting them read it, or it might be letting them write (make changes) to it, or lastly, allowing them to execute it (if it’s something that can be executed, like a script or an application).
Keeping these permissions safe is a pretty good idea. You might hear people talk about giving all their files 777 permissions. That’s the numerical representation of giving everyone access to do anything. This, in general, is not a good idea.
Do I know who my hosting provider is, and how to contact them?
It’s not as uncommon as you might think. Maybe you took over the site from someone else, or maybe the company you remember has long since changed names and domains.. it happens!
Identify your hosting provider
Navigate to HostingDetector.com
Navigate to https://hostingdetector.com/. This website allows you to search for a domain name’s hosting provider.
Identify your hosting provider.
Search for your domain name.
Identify your hosting provider.
The list of hosting information should include the following information:
a. Hosted by — The name of the hosting provider.
This link might not point directly to the hosting company’s website. Use your favorite search engine to search for the company website.
b. Country — The website’s country of origin.
c. WHOIS — A link to access domain registration information. Most website owners often use their hosting companies to register
What we learned:
A dedicated hosting environment is a computer that you have full control over.
A shared hosting environment is one in which you use a portion of a dedicated environment to host your website.
Maintaining a secure environment is the responsibility of the hosting customer as well as the hosting provider.
Content Management Systems, like WordPress and Joomla, require additional maintenance (like keeping them up to date) to ensure they remain secure.
SSL certificates are a good idea.
Complex passwords are valuable. Find ways of managing multiple passwords and use 2-factor authentication.
User input forms on a website can be vulnerable to SQL injection unless protective measures are taken.
Your file’s permissions can drastically impact your website’s security by instructing the system on the level of access that should be given to your website’s files.



